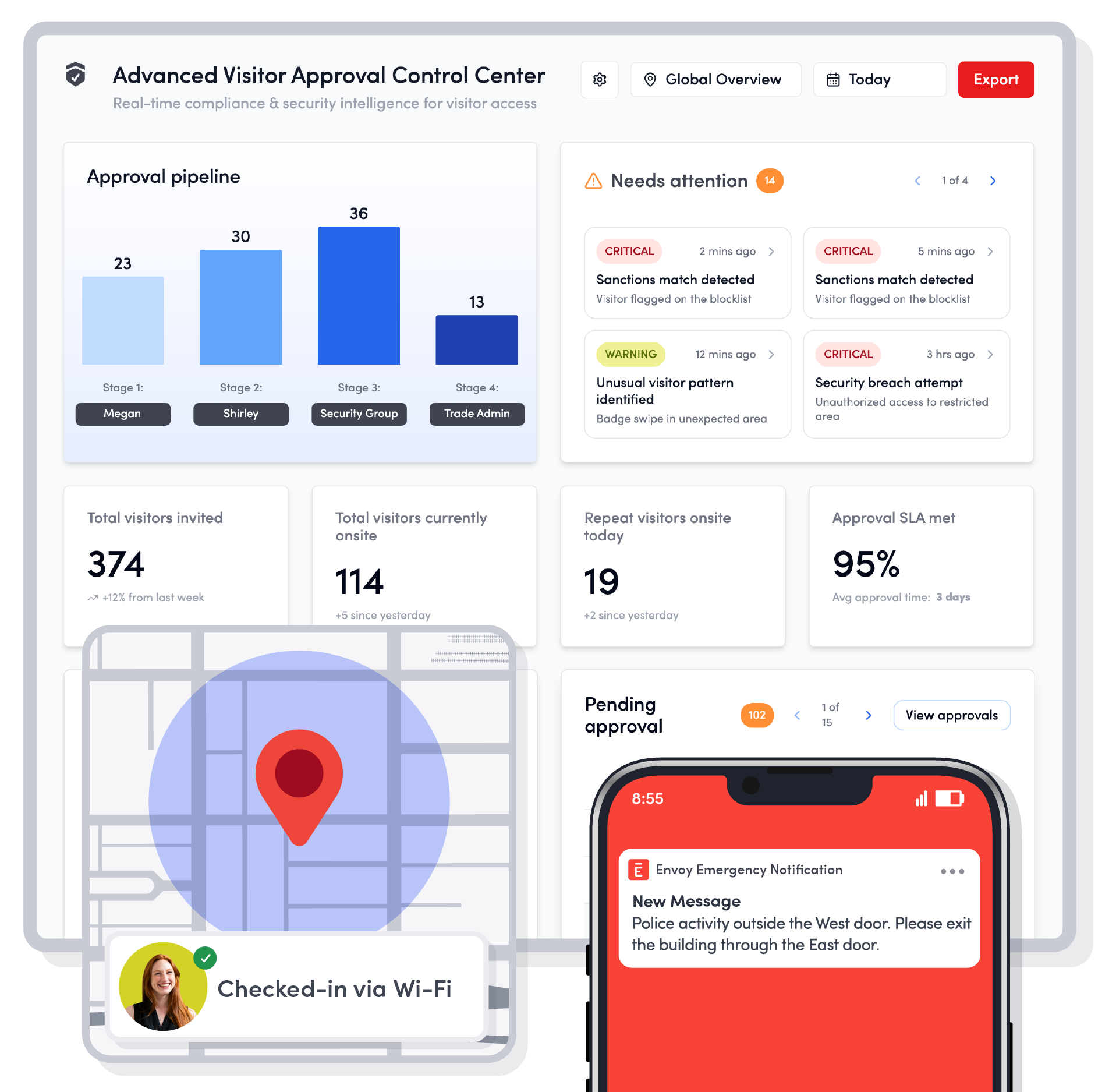
Proactively secure and protect your people and facilities
Envoy delivers multiple solutions on a single workplace platform—driving security, compliance, and safety, from visitor management to emergency notifications and onsite analytics.

Leverage integrations
Every workplace is different. Envoy adapts to yours with 100+ integrations with access control, communication platforms, and background screeners—so your team can move faster without switching apps.
Drive compliance
Skip the scramble before inspections. Envoy gives you the essential foundation to navigate the complex regulatory landscape and generate easy, audit-ready reports. Be audit-ready in minutes, not days.

Trust a market leader
For nearly 15 years, over 16,000 companies around the world have relied on Envoy to create safe, compliant, and welcoming workplace environments where their people can thrive every day.
Level up your safety and compliance strategy

How industry leaders automate screening & audits
Evolving export rules and rising global tensions make compliance more critical—and more complex—than ever. In this webinar, you’ll see how Parker Hannifin and Envoy automate visitor screening, access controls, and audits to protect sensitive facilities worldwide.

From reactive to resilient: The new compliance & safety playbook
The workplace is evolving fast. Remote work, new regulations, and rising risks make it harder than ever to stay compliant and secure. This playbook shows how forward-thinking organizations turn safety and compliance into a strength instead of a setback.
The must-have guide to workplace emergency planning
Be ready before disaster strikes. This guide walks you through how to prepare for emergencies, keep employees safe, and respond with confidence when every second counts.

Enhancing compliance and security
Global regulations are complex—and the cost of mistakes is high. This guide helps you understand key rules, avoid costly penalties, and keep your business moving without compliance headaches.

Why scattered systems put your biotech lab at risk—and how to stay audit-ready
A single breakdown in processes is a major security concern. Here’s how to mitigate risk.

From fragmented to full control: how manufacturers can build compliance resilience
Learn how to turn audits, safety, and regulatory oversight from a constant scramble into a competitive advantage.

