Visitor management for data centers
Control who comes onsite, maintain audit-ready logs, and protect every facility with a secure, modern visitor platform built for high-security environments.

The data center visitor system trusted by enterprise facilities





























Why data centers need a secure visitor management system
Between visitor, vendor, and technician sign-ins, operational load adds up fast. Manual processes make it tough to stay on top of security and maintain audit-ready records—leaving teams scrambling.
Strict access requirements
Unauthorized entry is a major threat. Data centers need a system that verifies identity, enforces pre-approvals, and ties every visit to the right areas and permissions.
Frequent contractor and tenant visits
Traffic is constant—from technicians to tenant customers. Without a clear workflow, teams lose visibility into who’s onsite, why they’re there, and whether they’re cleared.
High-stakes audit trails
SOC 2 and ISO standards demand accurate, time-stamped records. Spreadsheets and paper logs can’t deliver the consistency or retention auditors expect.
Badge management complexity
Managing temporary, time-bound, and visitor badges across multiple secure areas is complex. Manual workflows create bottlenecks and increase the chance of error.
Security-first visitor management for critical infrastructure
Envoy gives data centers a secure, automated way to verify visitors, manage access, and keep accurate records across every facility—all while keeping workflows tight and controlled.
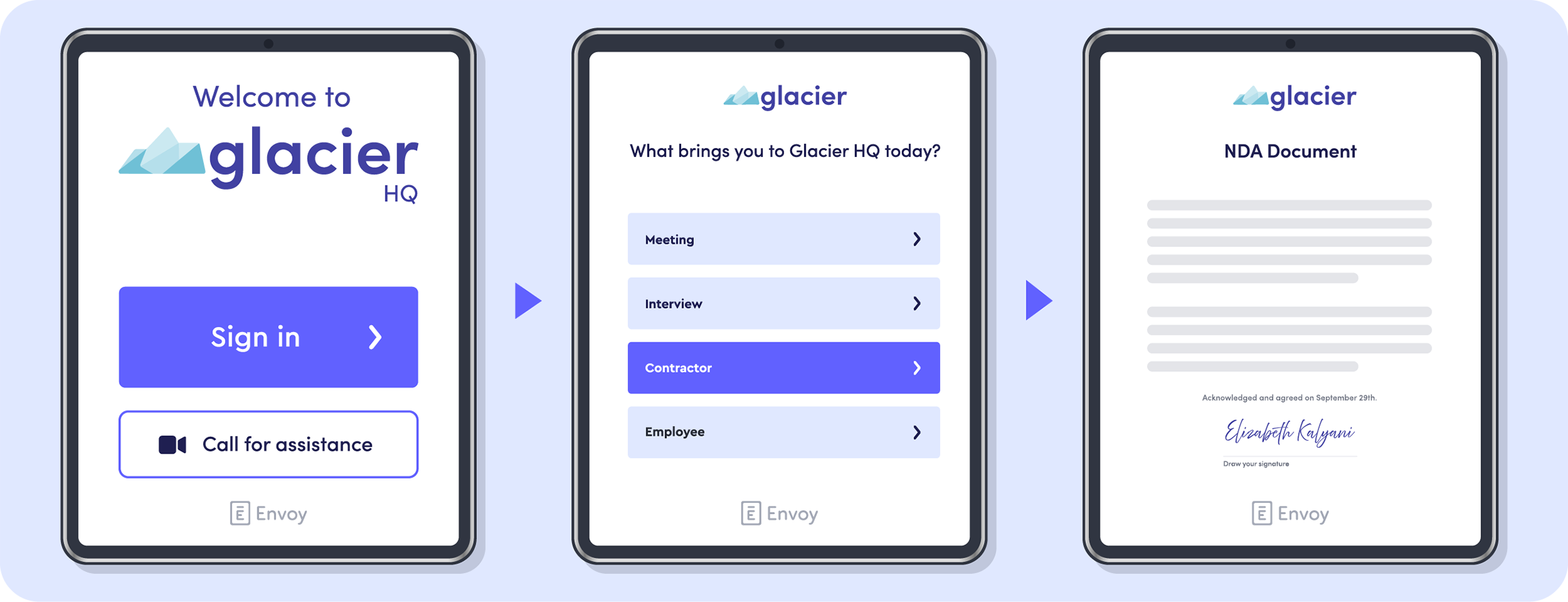
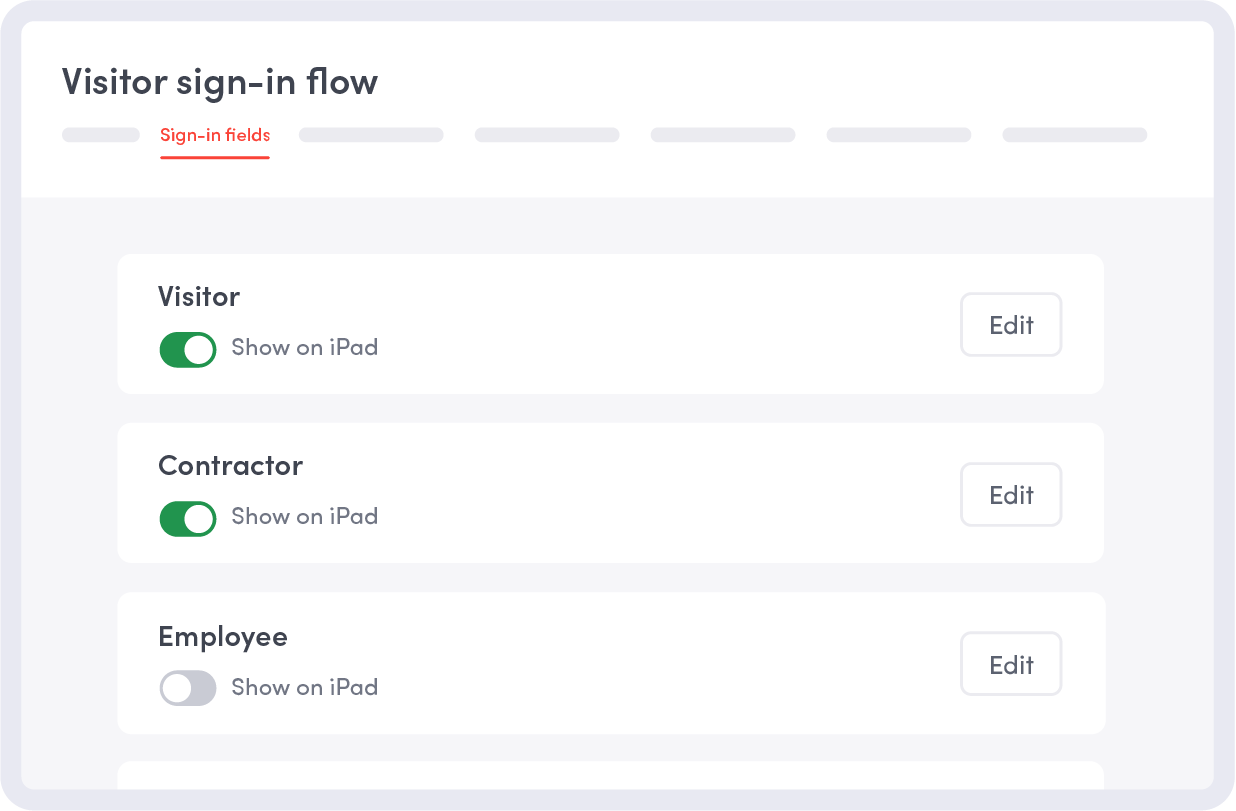
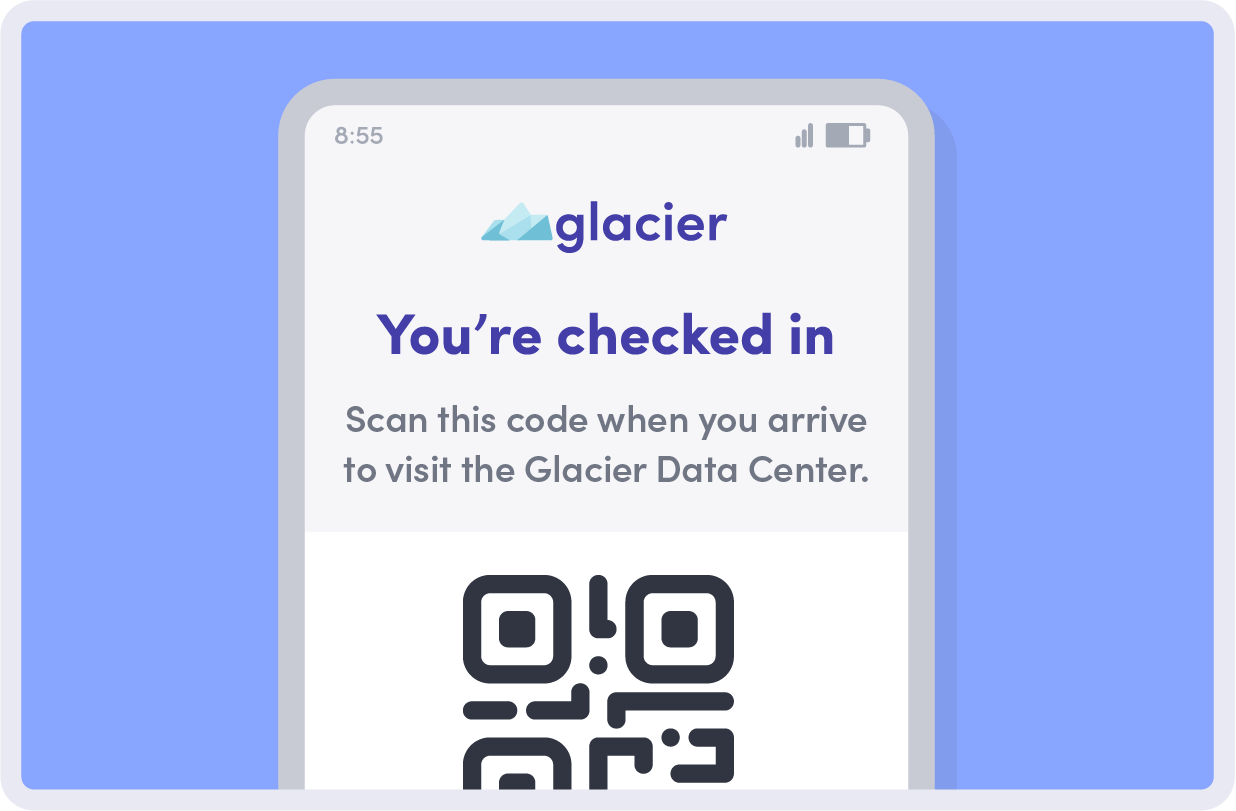
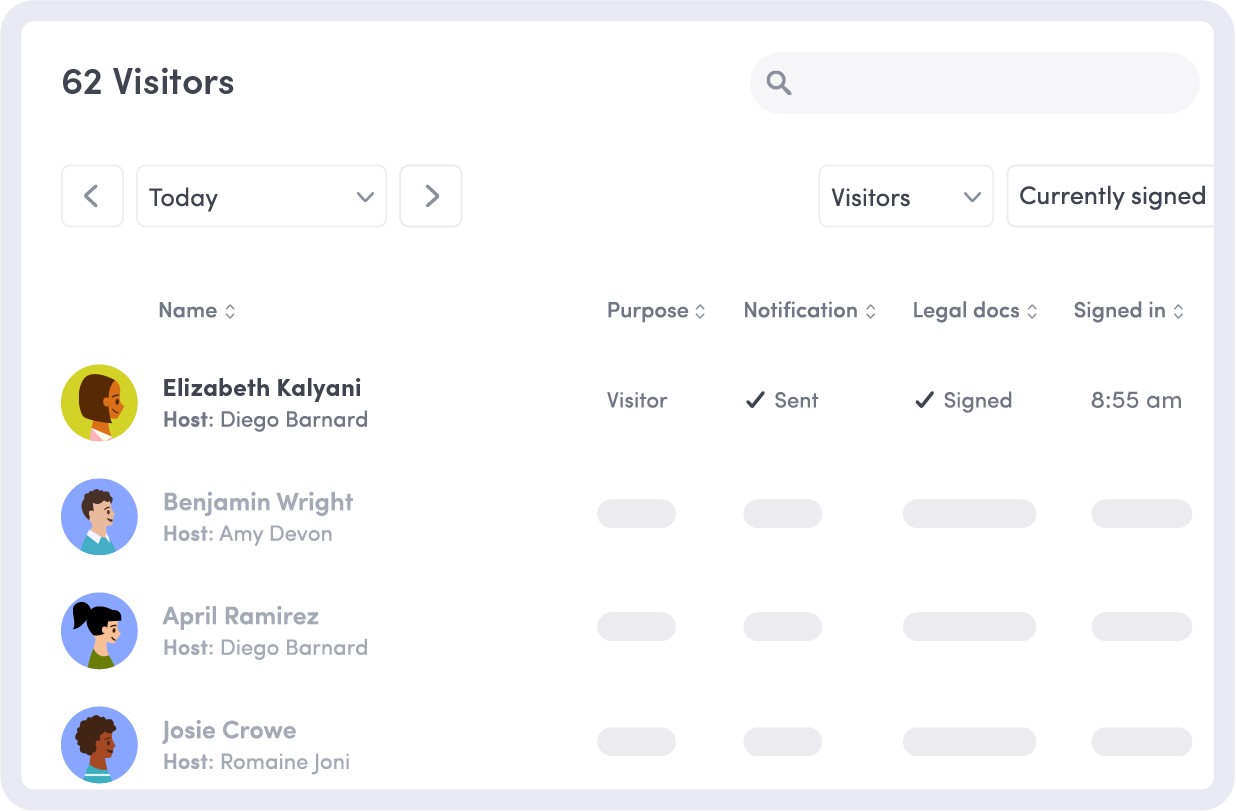
Secure, verified check-in
Capture IDs, require NDAs, and confirm visit details before anyone arrives onsite. Automated verifications ensure only approved individuals enter secure areas.
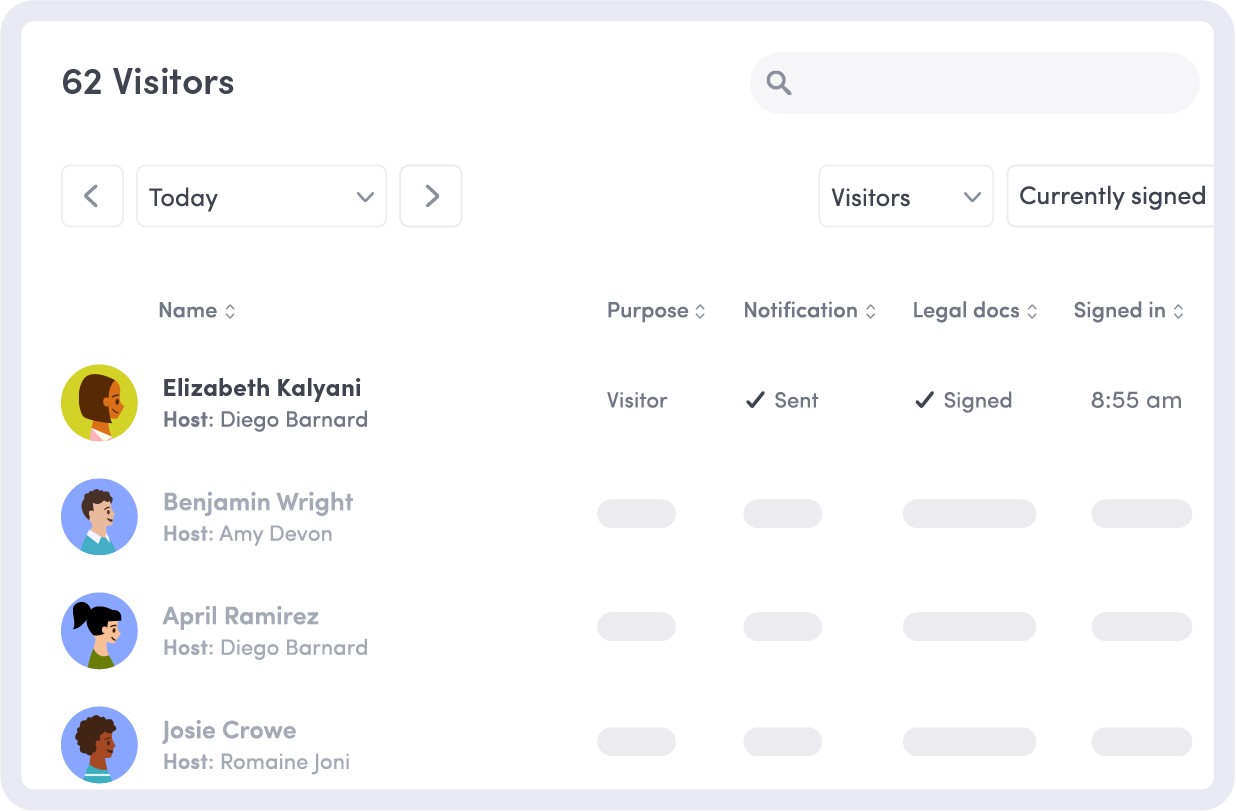
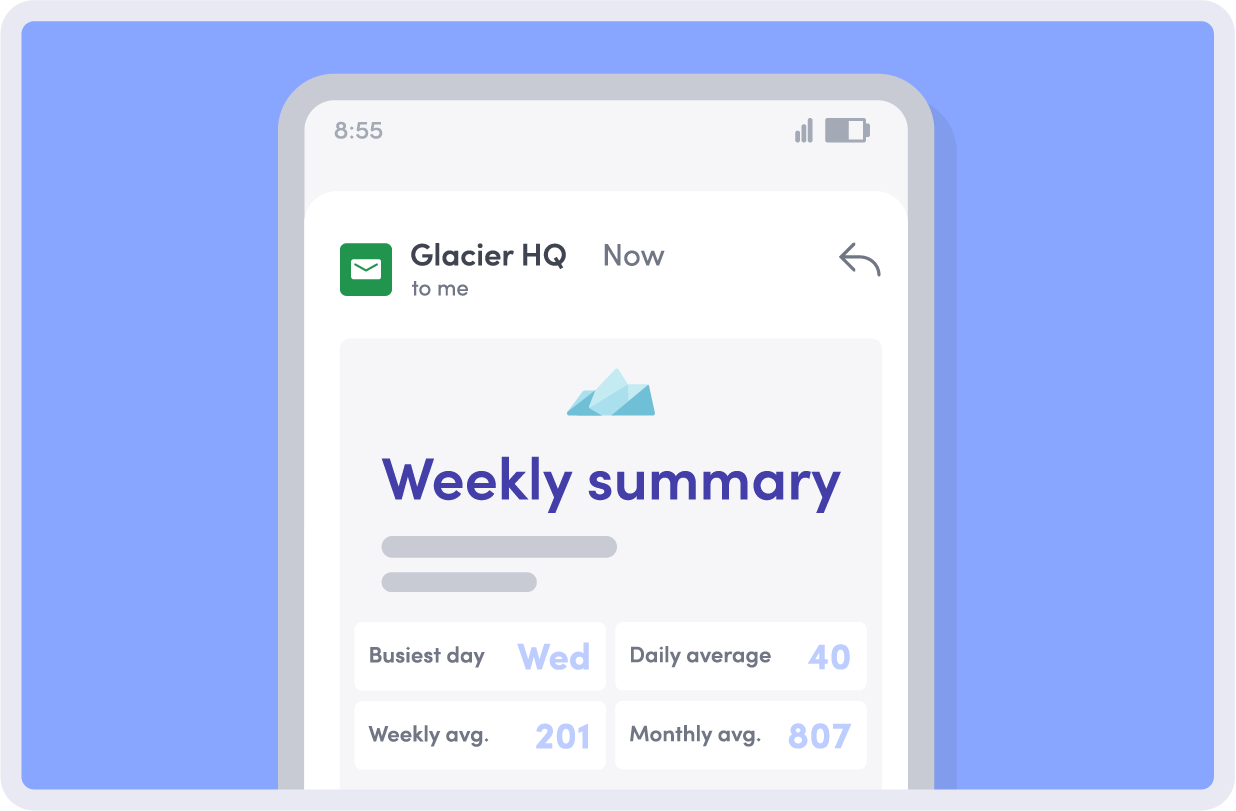
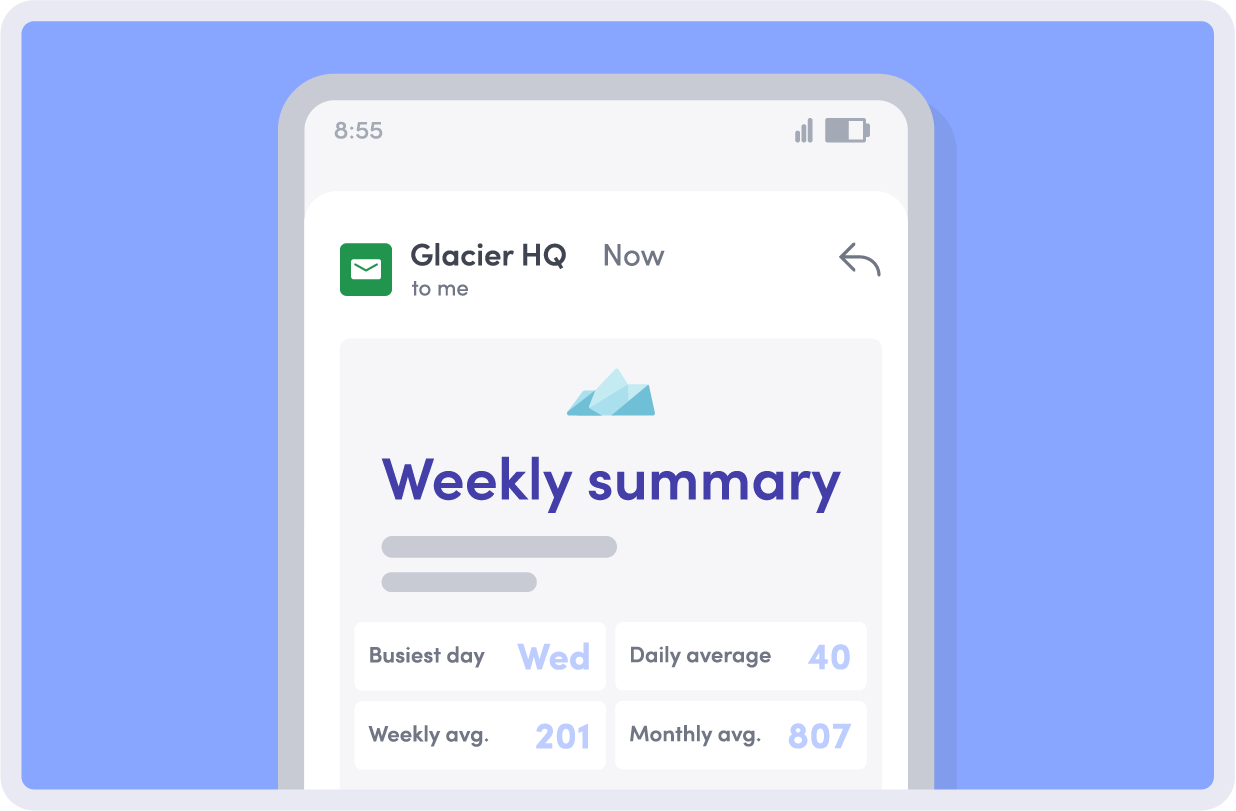
Automated audit trails
Envoy keeps detailed logs of who arrived, when they checked in, which areas they accessed, and who approved them—giving teams complete, audit-ready visibility.
Access control integrations
Sync visitor approvals with Brivo, LenelS2, or Openpath to issue time-limited badges, control restricted areas, and revoke access in seconds.
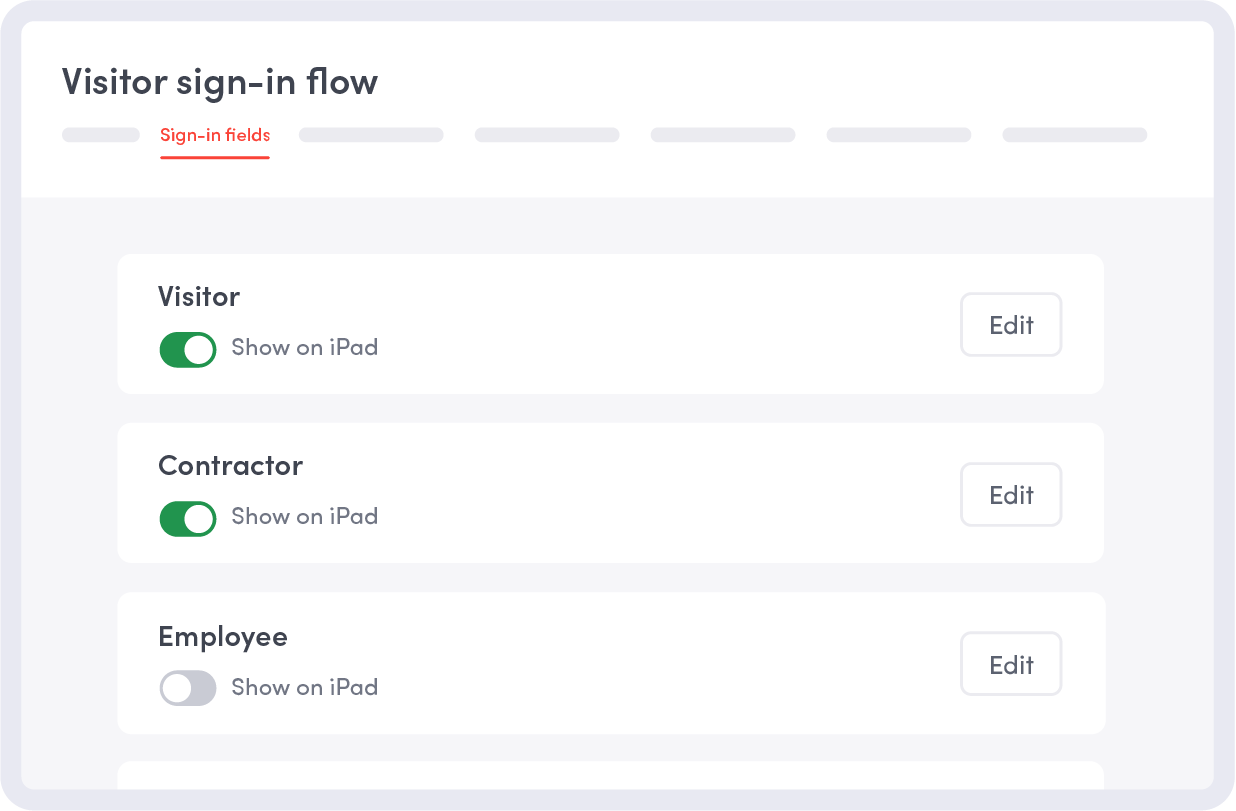
Contractor workflows with pre-registration
Pre-register vendors, assign required documentation, and confirm training or certifications before arrival so visits are smooth and secure.
How Envoy supports visitor management for data centers
Colocation visitor check-in
Manage tenant and customer visits with pre-approved workflows, identity verification, and clear access rules for shared spaces and secured areas.
Vendor + contractor access
Automate check-in, verify work orders, and ensure contractors meet documentation or safety requirements before accessing critical areas.
SOC compliance
Maintain accurate, time-stamped visitor records that align with SOC 2, ISO 27001, and other frameworks—reducing your audit prep time.
Restricted zone workflows
Define which areas your visitors can access, tie approvals to badges, and ensure sensitive areas stay locked down unless permissions are granted.
Multi-site access control
Manage visitor policies across multiple data centers. Standardize approvals, issue temporary credentials consistently, and export unified reports.

Colocation visitor check-in
Manage tenant and customer visits with pre-approved workflows, identity verification, and clear access rules for shared spaces and secured areas.

Vendor + contractor access
Automate check-in, verify work orders, and ensure contractors meet documentation or safety requirements before accessing critical areas.
SOC compliance
Maintain accurate, time-stamped visitor records that align with SOC 2, ISO 27001, and other frameworks—reducing your audit prep time.

Restricted zone workflows
Define which areas your visitors can access, tie approvals to badges, and ensure sensitive areas stay locked down unless permissions are granted.
Multi-site access control
Manage visitor policies across multiple data centers. Standardize approvals, issue temporary credentials consistently, and export unified reports.


Trusted by data centers

FRANK KOTRUS
Group Vice President of Technical Operations at Raxio Group
Run your data centers from one workplace ecosystem
Reservations
Unlock controlled booking with built-in workplace analytics. Track every reservation, monitor usage across sites, and use real data to support audits and operational decisions.
Learn about Envoy Reservations

Visitors
Streamline secure check-ins, enforce approvals, and maintain audit-ready logs that support compliance and business continuity.
Learn about Envoy VisitorsEmergency Notifications
Notify onsite teams and contractors instantly during outages, maintenance events, or security incidents.
Learn about Envoy’s Emergency Notifications
Still have questions?
We can help.
A data center visitor system ensures only authorized visitors, vendors, and contractors can access your space. It handles ID checks, pre-approvals, badge management, and audit-ready logs to keep your facilities secure.
Envoy keeps detailed, exportable visit records, enforces approvals, and makes it easy to stay on top of SOC 2, ISO 27001, and other data center compliance requirements—so audits are simpler and stress-free.
Yes. Envoy makes it easy to pre-register contractors, verify their identity, check required documents, and grant time-limited access—keeping vendor activity secure and compliant.
Envoy offers secure access control integrations—including Brivo, LenelS2, and Openpath—so you can issue temporary credentials, enforce zone restrictions, and instantly revoke access when a visit ends.
Visitor data is protected with encryption, role-based permissions, and strict retention policies. Envoy also keeps full audit trail visitor logs, making it easy to see who checked in, when, and where.
Yes. Envoy can issue time-limited visitor badges, sync with access control for credential activation, and track badge status across facilities.
Visitor management software helps data centers track and control who enters secure facilities. Envoy ensures employees, visitors, vendors, and contractors are pre-registered, approved, and checked in efficiently while maintaining compliance with SOC, SOC2, FedRAMP, GDPR, ISO 27001, OSHA, California SB 553, and PCI DSS requirements.
Envoy provides a real-time view of everyone onsite, including employees, vendors, contractors, and visitors. This helps teams monitor occupancy, respond quickly during incidents, and maintain audit-ready records for compliance and security reviews.
Yes. Admins can pre-register any visitor and assign multi-step approvals before arrival. This reduces front-desk wait times, ensures proper access, and keeps data center operations secure and efficient.
Envoy logs every visitor with timestamps, approvals, and access history, providing audit-ready records. These logs support SOC, SOC2, FedRAMP, GDPR, ISO 27001, OSHA, California SB 553, and PCI DSS and other regulatory frameworks, reducing manual paperwork and improving traceability.
Envoy enforces time-bound access, badge printing, and escort rules for restricted areas. Real-time monitoring and visitor logs help prevent unauthorized entry, respond quickly to incidents, access historical information and enforce block lists, and maintain a safer, more controlled environment.
Facility managers, security teams, compliance officers, and operations leaders benefit from real-time visibility and streamlined check-in processes. Employees, visitors, vendors, and contractors experience smoother access while the organization maintains a secure and compliant environment.


